Solutions de gouvernance de l'information
Everteam édite une offre logicielle unique, capable de combiner l'analyse intelligente de contenus et la gestion du cycle de vie jusqu’à l’archivage sécurisé.
Pourquoi la gouvernance de l’information
La mission d’Everteam est d’accompagner les entreprises dans leur transformation digitale, maintenir l’intégrité de leur gestion & politique documentaire et s’inscrire dans une approche de sobriété numérique.
Nous aidons les entreprises :
- à valoriser et assainir leurs documents et données quelles que soient leur source et format,
- à gérer et sécuriser leur capital informationnel, notamment contre les risques liés à la confidentialité des données ou la conformité réglementaire (RGPD, cycle vie).
Data need to be sure

You don’t want to be mess with the law

Increase adaptability

There’s simply too much data

It’s not all good data

You can’t keep it all in once place

It’s hard to find the right data
Retrouver l'information importante plus vite

Réduire les risques (réglementaire, confidentialité, sécurité)

Assainir et réduire les coûts de stockage

Archiver de manière sécurisé, intègre et pérenne

Améliorer la qualité des données

Piloter les cycles de vie de l'information où qu'elle se trouve

Aller vers le numérique responsable
Nos solutions IG Suite
Nous recommandons la mise en place d’une gouvernance de l’information et un archivage sécurisé en conformité avec les normes en vigueur.
Ceci afin d’intervenir sur l’assainissement et la gouvernance du vrac numérique, l’analyse/classification automatique de contenu via une recherche multicanal (360°).
RECHERCHER
Unified Search & Content Explorer
Se connecter aux référentiels de contenu pour rechercher et trouver, et naviguer dans l’univers de votre contenu
ANALYSER
File Analysis
Nettoyer, enrichir et remédier au contenu de vos référentiels de contenu.
GOUVERNER
In Place Records Management
Définissez vos politiques de cycle de vie de l’information et appliquez-les à vos référentiels de contenu.
ARCHIVER
Electronic Archiving System
Gérer vos documents, dossiers et archives, les préserver et les sécuriser à long terme, respecter les normes d’archivage.
Nos clients






Ils l’ont dit
Suite à un important problème de conformité des informations,nous avons dû en urgence pouvoir nettoyer un lot de documents. Nous avons testé everteam.discover. brillamment en quelques mois avec d’excellents résultats et l’avons ensuite déployé sur d’autres cas d’usages

Le but de la mise en place d'un système d'archivage électronique était de centraliser davantage l'information stratégique et sensible au sein du groupe et puis de pouvoir garantir toute la gestion des risques au niveau de son accessibilité, et de sa disponibilité.

Avec la première mise en œuvre du référentiel de conservation, nous avons eu un gain estimé de 30 % de volume parce qu'il y avait peu de pratique de destruction avant ce projet.

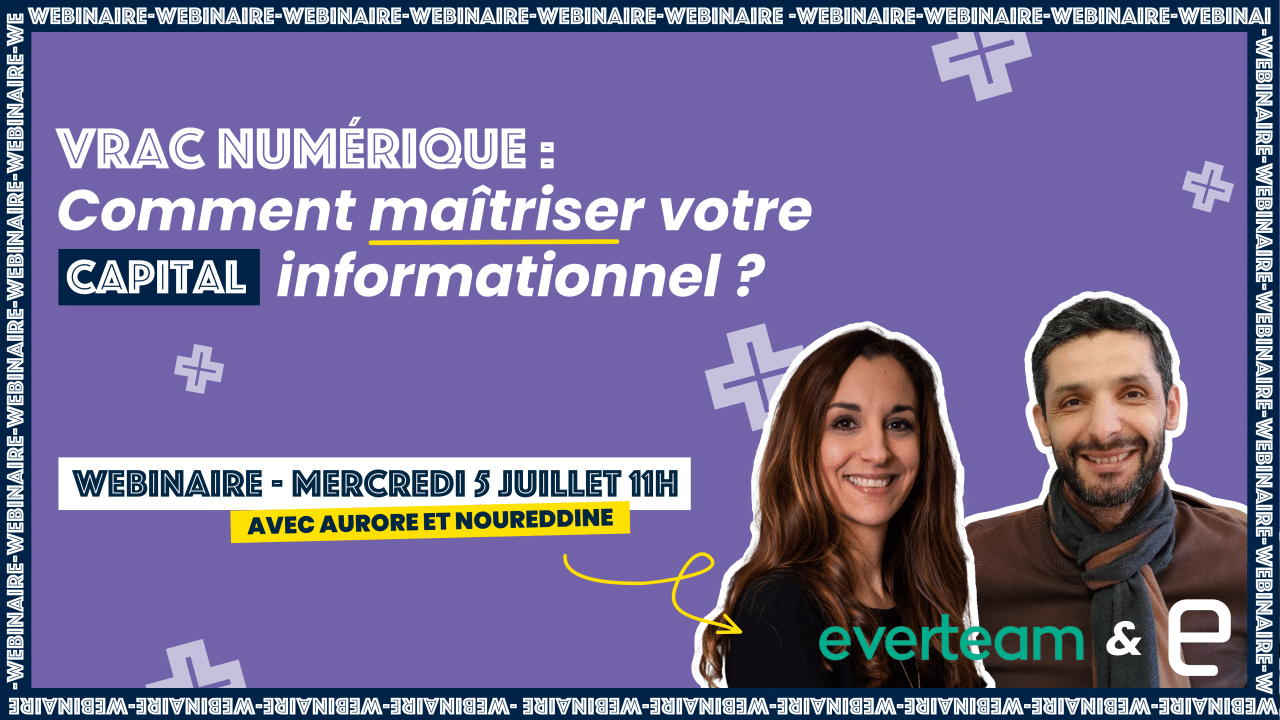
Nos ressources
Vous souhaitez en apprendre plus sur le secteur de la gouvernance de l’information ? Consultez nos ressources.
Nos évènements
Vous avez un projet ?